An audit does not fail overnight.
It expires quietly.
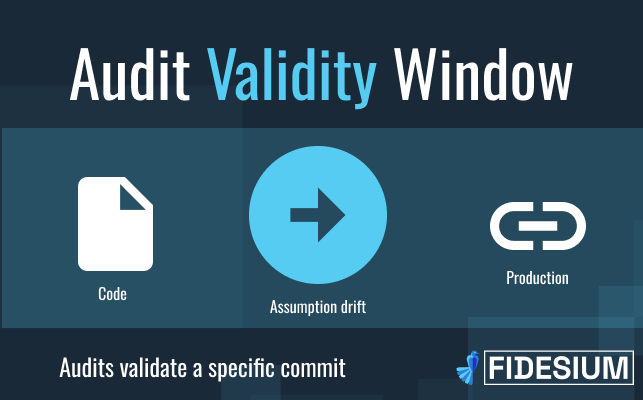
Most Web3 teams treat “Was Audited” as a durable security signal. But a smart contract audit validates a specific version of code, under a specific set of assumptions.
And those assumptions rarely stay static. So the real question isn’t whether audits are important. It’s this:
When does a smart contract audit actually expire?
What Does a Smart Contract Audit Actually Validate?
A smart contract audit validates:
- A specific commit hash
- A defined contract architecture
- A particular access control structure
- A given dependency set
- A documented set of invariants and assumptions
- Known trust boundaries at that point in time
A smart contract audit is precise. But it is version-bound.
It confirms:
“Given these assumptions and this code state, no critical vulnerabilities were identified.”
It does not guarantee safety across future upgrades, integrations, or governance changes.
A web3 audit is not a permanent security state.
It is a validation of assumptions at a specific moment.
When Does a Smart Contract Audit Expire?
A smart contract audit expires when certain code is changed or the assumptions it validated no longer match the live system.
This does not always happen dramatically. It often happens gradually.
Audit expiration occurs when:
- Core invariants are modified
- Role permissions change
- Governance parameters shift
- New external integrations are added
- Dependencies are upgraded
- Trust boundaries expand
- Contract architecture evolves
The key issue is not code change alone. It is assumption change.
If assumptions change, validation must change.
What Is Audit Assumption Drift?
Audit assumption drift occurs when the assumptions validated during an audit no longer reflect the current production environment.
It is rarely visible at first.
- Tests still pass
- Deployments succeed
- No alarms trigger
But the risk model has shifted.
For example:
- A governance contract originally assumed limited admin roles. Later, a new multi-sig or delegated role is added.
- A dependency is upgraded, introducing subtle state-handling differences.
- An external oracle is integrated without being part of the original trust model.
- A liquidity routing function expands exposure to new contract paths.
None of these changes necessarily break the system immediately.
But they invalidate parts of the original audit reasoning.
Audit expiration is usually silent.
It’s the result of accumulated assumption drift.
Do All Code Changes Invalidate an Audit?
No. Not every change requires a full re-audit.
There is a difference between incremental updates and structural risk shifts.
Changes that often do NOT require a full re-audit:
- UI updates
- Gas optimizations
- Comment edits
- Non-sensitive refactors
- Internal code organization improvements
Changes that often DO require deeper review:
- Modifying core invariants
- Changing role or permission logic
- Adding new external contract calls
- Introducing new cross-contract trust dependencies
- Altering custody logic or fund flow mechanics
The right question is not:
“Did we change code?”
t is:
“Did we change assumptions?”
Security scope should follow structural risk, not update frequency.
Why Is Audit Expiration a Governance Risk?
Audit expiration is not just technical, it is governance-level.
When projects claim:
“We were audited.”
Investors, exchanges, and users assume that validation reflects the current system.
Without version context, that claim becomes ambiguous.
Versionless audit statements can create:
- Diligence friction during fundraising
- Additional scrutiny during exchange listings
- Slower institutional onboarding
- Credibility gaps after incidents
Security posture must evolve alongside releases.
Otherwise, the audit becomes archival, not operational.
A time-bound audit treated as permanent creates governance ambiguity.
Are Full Re-Audits Always Necessary?
Full re-audits are sometimes necessary, especially when structural risk changes. But many updates affect limited portions of code.
Resetting validation from scratch every release is expensive and inefficient.
Traditional audit models often force a binary choice:
- No review
- Full re-audit
Modern development cycles don’t operate in binaries.
Web3 teams ship weekly, sometimes daily. Security validation must operate at the same velocity.
How Should Smart Contract Security Evolve After an Audit?
Security validation should evolve alongside code changes.
That means:
- Tracking assumption changes
- onitoring diffs instead of rescanning unchanged logic
- Detecting regression against previous findings
- Integrating security into CI/CD workflows
- Preserving version-linked validation history
This does not mean replacing auditors with automation.
It means embedding audit expertise into development workflows.
The strongest model combines:
- Auditor-authored detection logic
- Dev-integrated tooling
- Human validation where judgment and business logic reasoning are required
Automation handles scale.
Auditors handle intent.
Together, they preserve audit credibility over time.
What Is the Future of Smart Contract Audit Validity?
The future of smart contract security is version-aware.
Audits will remain critical.
But their value must compound, not reset.
Security must shift from:
- Static report → living validation
- Point-in-time → version-linked
- External event → integrated workflow
In Web3, security is not a binary state.
It is a continuously evolving contract between:
- Code
- Assumptions
- Validation
Audits don’t fail.
Assumptions drift.
The teams that track that drift and validate against it continuously, preserve both security and credibility.
FAQ
When does a smart contract audit expire?
A smart contract audit effectively expires when the assumptions validated during the audit no longer match the live production system. This typically occurs after structural code changes, new integrations, role modifications, or dependency upgrades.
Do all smart contract updates require a new audit?
No. Minor updates such as UI changes or internal refactoring may not require a full re-audit. Structural risk changes, such as altered invariants, new trust boundaries, or modified permission logic, typically require deeper review.
What is audit assumption drift?
Audit assumption drift occurs when incremental changes to a system gradually invalidate the assumptions originally validated during an audit. It often happens silently and becomes visible only after an exploit or security failure.
Is continuous validation better than periodic re-audits?
Continuous, version-aware validation preserves audit credibility between releases and reduces unnecessary re-audits. However, major architectural changes still require human-led audit review. The strongest security model combines both.