Security as a process allows companies to launch quickly and on schedule.
In the world of blockchain and Web3 development, security is not merely a checkpoint but a continuous process. When done correctly it empowers organizations to innovate boldly while mitigating risks. This approach transforms potential vulnerabilities into opportunities for refinement, allowing PB&J to launch products on schedule without compromising quality or safety. At Fidesium, we specialize in providing proprietary audit tooling that integrates seamlessly into this process, enabling clients to identify and resolve issues early. The following case study illustrates these principles through our collaboration with PB&J Consulting, one of our longest-standing partners, on the successful deployment of their groundbreaking product, Trivi Agent.
PB&J consulting
https://pbandjweb3.com/
Established as a premier partner in the Web3 ecosystem since its inception. Positioning themselves as more than a traditional advisory firm, PB&J emphasizes hands-on execution, embedding their team directly with clients to drive tangible results. Their services span a comprehensive suite tailored to blockchain and digital asset ventures, including:
- Tokenomics and Architecture Design: Crafting token models that prioritize governance, utility, and long-term value alignment with business goals.
- Unified Launch Services: Deploying multidisciplinary teams comprising investors, executives, marketing specialists, and digital asset experts to orchestrate high-impact token launches.
- Treasury Management: Offering sophisticated strategies for market-making, on-chain liquidity, and investment to support both immediate operational needs and sustained growth.
- Strategic Partnerships: Leveraging an extensive network within the Web3 community to foster collaborations, identify investment opportunities, and incubate innovative ideas.
Trivi Agent
https://triviagent.ai/
A revolutionary blockchain native, token powered PVP Trivia game. By using our proprietary audit tooling they went from MVP to live deployed product in under a month, while avoiding significant security flaws in the process.
| 📁 | TriviTournament/ | 6/11/2025 | 9:58:44 PM | |
| 📁 | TriviTournamentSinglePlayer/ | 6/26/2025 | 2:34:30 PM | |
| 📁 | TriviTourney/ | 6/03/2025 | 8:54:18 PM | |
| 📁 | TriviTourneyLeaveUpgrade/ | 6/25/2025 | 2:07:53 PM |
Case Study Overview
Having addressed the preliminary matters, we are pleased to present an overview of a case study focused on security, wherein we will highlight a couple key issues identified and provide a general understanding of how automated tools can effectively detect such intricate challenges. While we will refrain from delving into excessively granular details, due to time restraints and not giving too much away, we invite you to explore a broader examination of the underlying processes.
Gas Bomb/DoS in unbounded loop
The contract was iterating over an unbounded loop potentially exceeding the gaslimit. This opened the contract up to all manner of failure states, from sybilled DDoS/Griefing, to just accidental “victim of own success” situations based on huge player counts.
We ultimately recommended a two phased approach, one was loop pagination, and the other was the extraction of resource intensive contract calls into its own manipulation function and adoption of a pull over push model on these side effects.
So, how did we build a tool to identify these flaws and to make recommendations on them, in under a minute?
1. Fidesium breaks down the contract into its AST
2. Identify any loop nodes
3. Check if the loop is protected
Whether it’s bound is dynamic rather than constant. We validate a variety of protection mechanisms – require calls, assert calls, early returns, try catch blocks, custom modifiers and apply a mix of Signature based detection and Data Flow analytics to identify complex conditions such as:
if (arr.length > 100) return;
4. Validate whether the loop body conducts any expensive operations.
We flag contract calls, struct assignments, nested function calls, mapping updates, and many other side effects, applying abstract interpretation modelling across intraprocedural scenarios, allowing us to track variable assignments as Abstract State representations.
We then serve a digest of the above to our customers, alongside AI generated recommendations on improvements and next steps.
5. Ease of use and ease of review
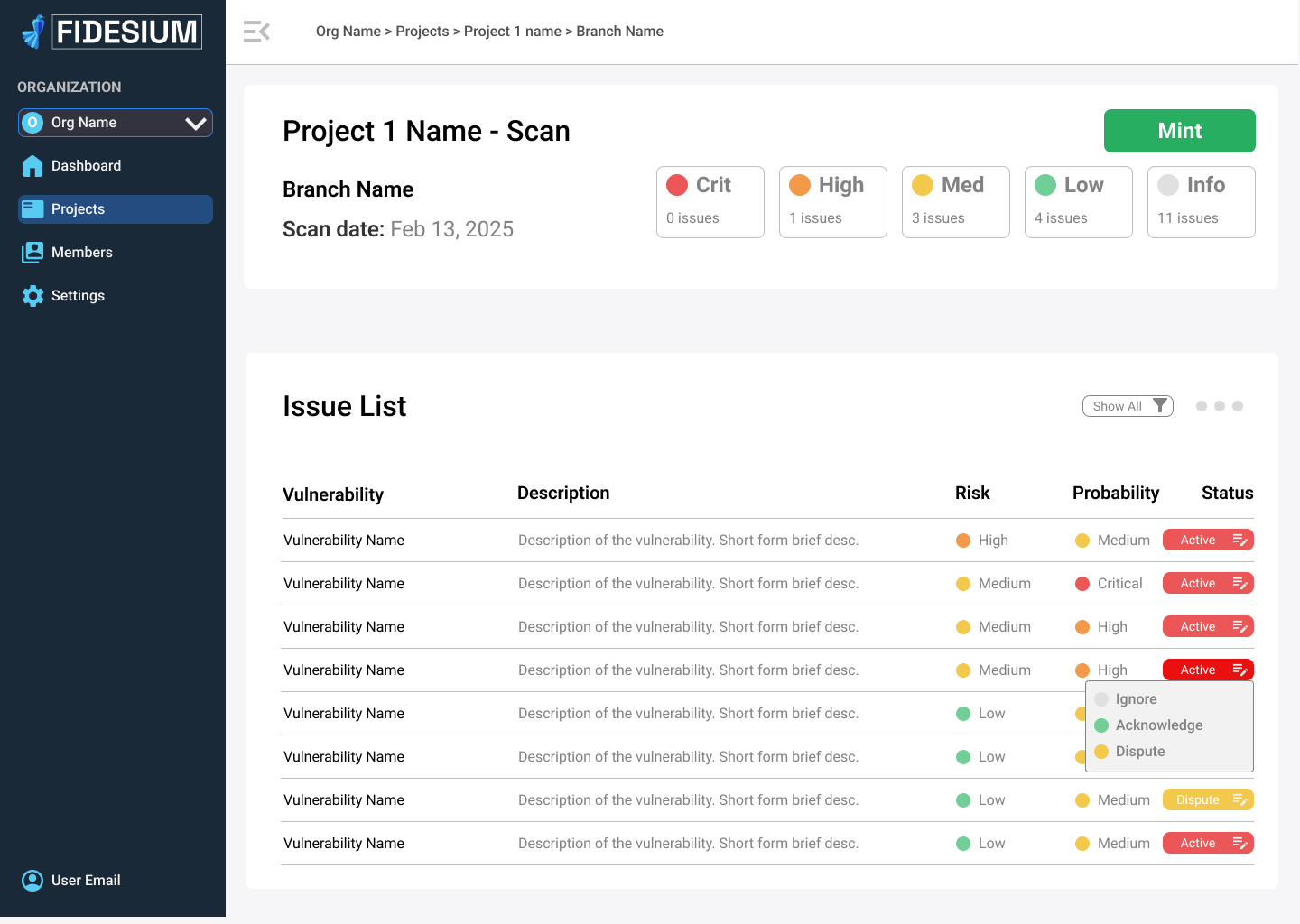
Finally, we provide this data to our customers in an easy to use and understand dashboard allowing real time responses and resource allocation to be built directly into your SDLC.
Why does this approach work?
By relying on traditional, mathematically sound computer science techniques, we avoid false positives and hallucinations, and deliver a result that’s quick, consistent, independent of AI token costs or hype cycles. While we do rely on LLMs to generate human readable digests, we do have fallback mechanisms that are admittedly slightly more generic but still convey the core technical details of the vulnerability. As a result, we can go from button press, to fully audited contract, in under 5 minutes. This lets our customers hit the ground running, and deliver software from whiteboard to production in a matter of months, bypassing expensive time commitments to auditor queues. Oh and best of all, this cost our customer under 1200$. (Yes we do also do manual audits, no you probably don’t need one (watch this space for a link), yes they are charged separately).